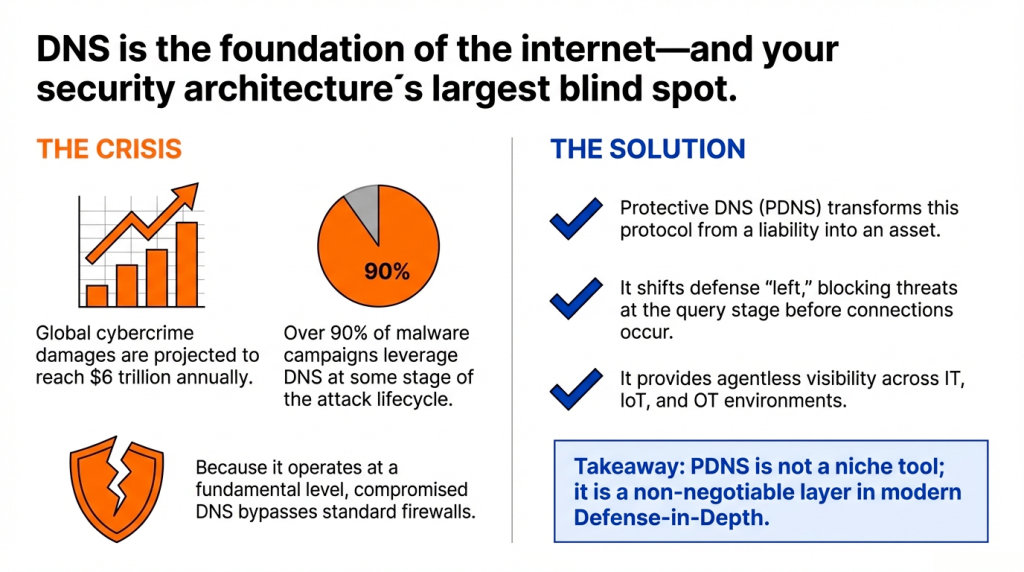
The Domain Name System (DNS) is the foundational address book of the internet, a ubiquitous and trusted protocol that underpins virtually all online activity, from browsing websites to sending emails. This inherent trust and ubiquity, however, make it a primary target for cyberattacks, with global cybercrime damages projected to reach $6 trillion annually. Because it operates at a fundamental level that many security tools overlook, a compromised DNS can become an organization’s most significant blind spot. This article will demystify Protective DNS (PDNS), explaining what it is, its critical role in a modern defense-in-depth strategy, and five powerful examples of how it protects an organization from a wide array of cyber threats.
1. The Internet’s Address Book: Understanding DNS and Its Inherent Risks
Before an organization can secure its DNS traffic, it must first understand the fundamental role of DNS and why its default design creates significant security blind spots for traditional defense tools. DNS is the core mechanism that translates human-readable domain names, like www.example.com, into the machine-readable IP addresses that computers use to connect to one another. It functions much like an address book for the internet, making navigation seamless and intuitive for users.

However, this essential service is also a common security weakness for three core reasons:
- It is ubiquitous. Every type of internet request—from web browsing to cloud computing—relies on DNS. This makes it an ideal channel for attackers to exploit.
- It was designed to resolve, not to judge. Standard recursive DNS was built only to resolve requests, not to evaluate whether the destination is safe or malicious. It blindly connects users to any requested domain, including those hosting malware.
- Attackers exploit this blind spot on port 53. Traditional firewalls do not typically inspect traffic on port 53, the standard channel for DNS queries. Attackers use it as a covert channel to bypass traditional perimeter defenses.
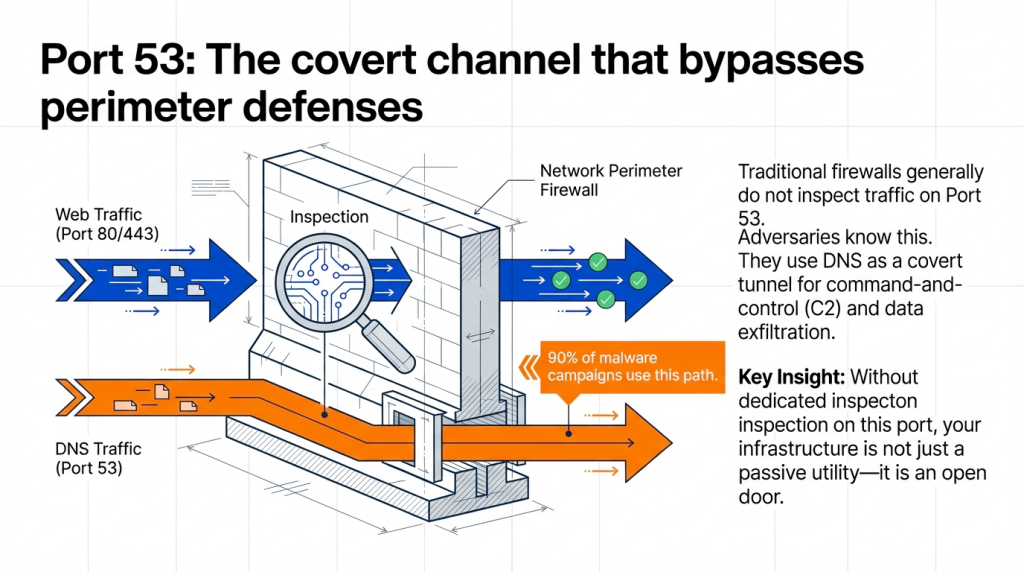
The scale of this threat is staggering; research shows that over 90% of malware campaigns leverage DNS at some stage of their attack lifecycle. Without dedicated protections, an organization’s DNS infrastructure is not just a passive utility—it’s an open door for adversaries. This reality necessitates a strategic shift from treating DNS as a simple resolver to leveraging it as a proactive security control.
2. From Passive Resolver to Proactive Defense: Defining Protective DNS
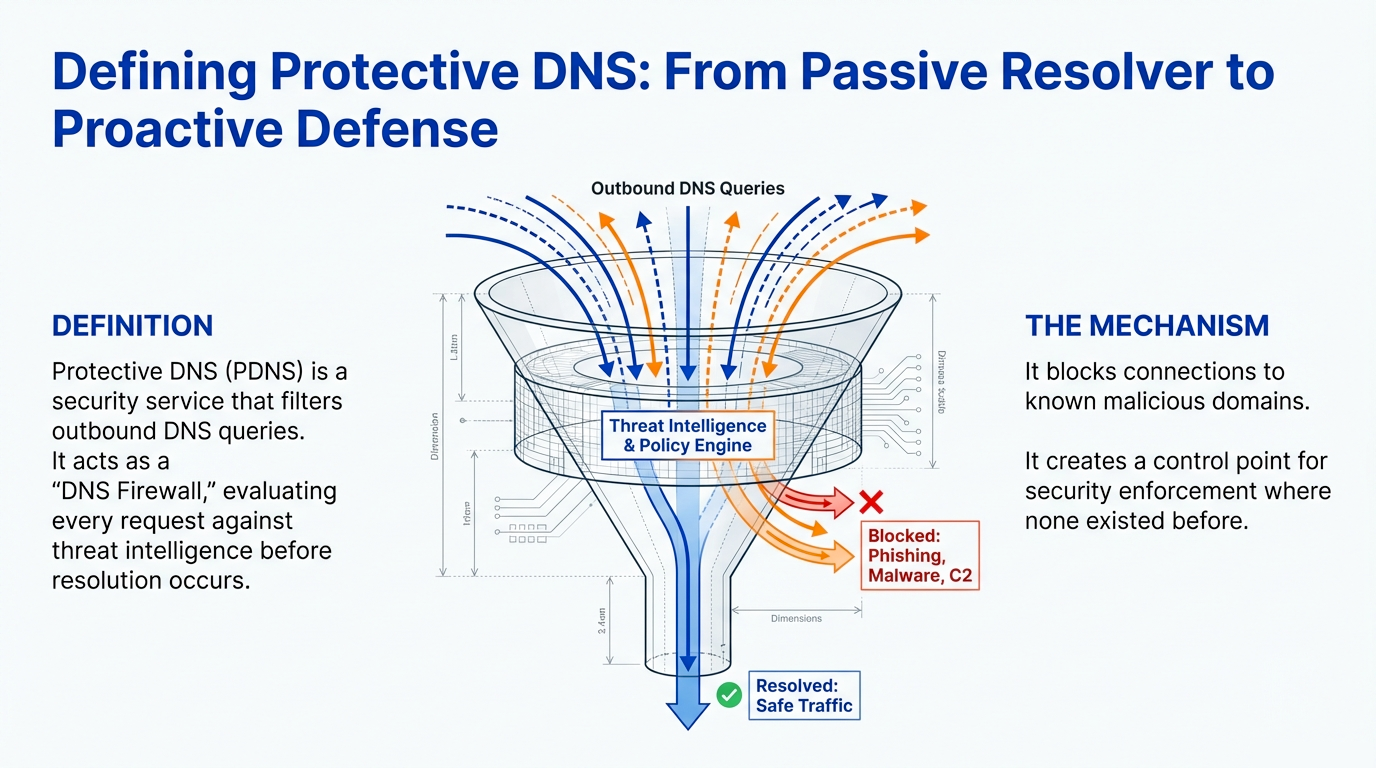
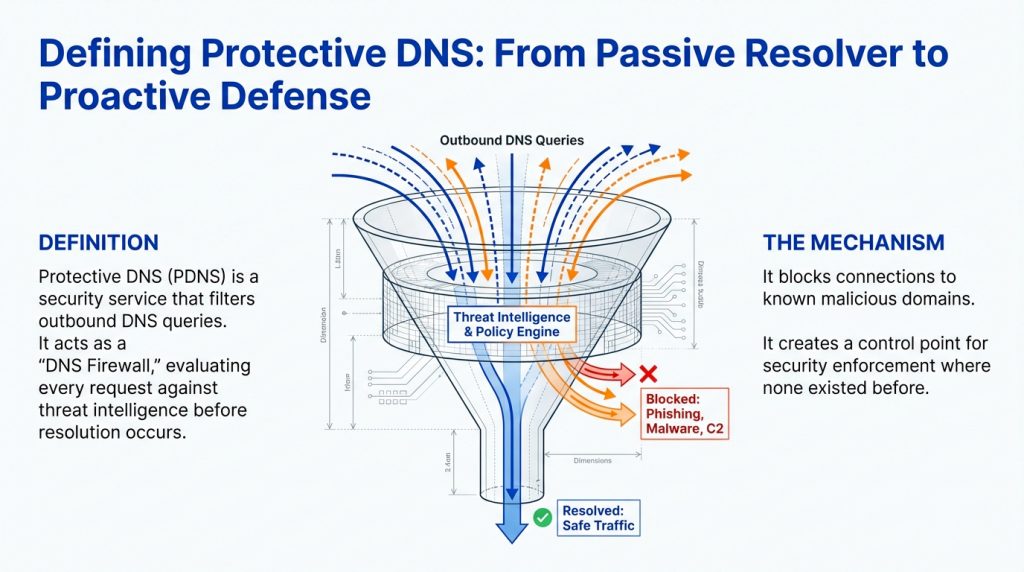
The strategic evolution of cybersecurity involves transforming foundational protocols from potential liabilities into active defensive assets. This is precisely the role of Protective DNS (PDNS), which reframes DNS from a simple name-resolution utility into a critical control point for security enforcement.
Protective DNS (PDNS) is a security service that filters an organization’s outbound DNS queries to block connections to known or suspected malicious domains. Often referred to as a “DNS firewall,” it acts as a powerful first line of defense, preventing users and devices from ever reaching harmful destinations on the internet.
A key distinction between PDNS and traditional network firewalls lies in when they act.
- Protective DNS blocks threats before an IP connection is ever established. It intervenes at the earliest stage of a network request—the domain name lookup.
- Conventional Firewalls inspect traffic after DNS resolution has already occurred and a connection to a potentially malicious IP address is being attempted.
The core mechanism of PDNS is straightforward yet powerful. It evaluates every outgoing DNS query against comprehensive, continuously updated threat intelligence feeds containing vast lists of domains associated with phishing, malware, and command-and-control (C2) servers. If a query matches a malicious entry, the PDNS service blocks the request.

Crucially, modern PDNS services move beyond reactive blocklists by using machine learning (ML) and behavioral analysis to become predictive. Their primary value lies in their ability to algorithmically identify previously unseen malicious domains. By analyzing attributes like high textual entropy, these systems can proactively block threats that use Domain Generation Algorithms (DGAs) to evade static defenses. This proactive blocking “shifts left” in the attack cycle, neutralizing threats at the earliest possible moment and easing the burden on downstream security controls like firewalls and Endpoint Detection and Response (EDR) tools—a key strategic benefit for resource-strapped security teams.

3. Five Critical Use Cases: How Protective DNS Defends Your Organization
We will now explore five practical, high-impact examples that demonstrate how Protective DNS moves from a theoretical concept to a tangible security asset that stops real-world attacks. These use cases highlight its versatility and critical role within a layered defense strategy.
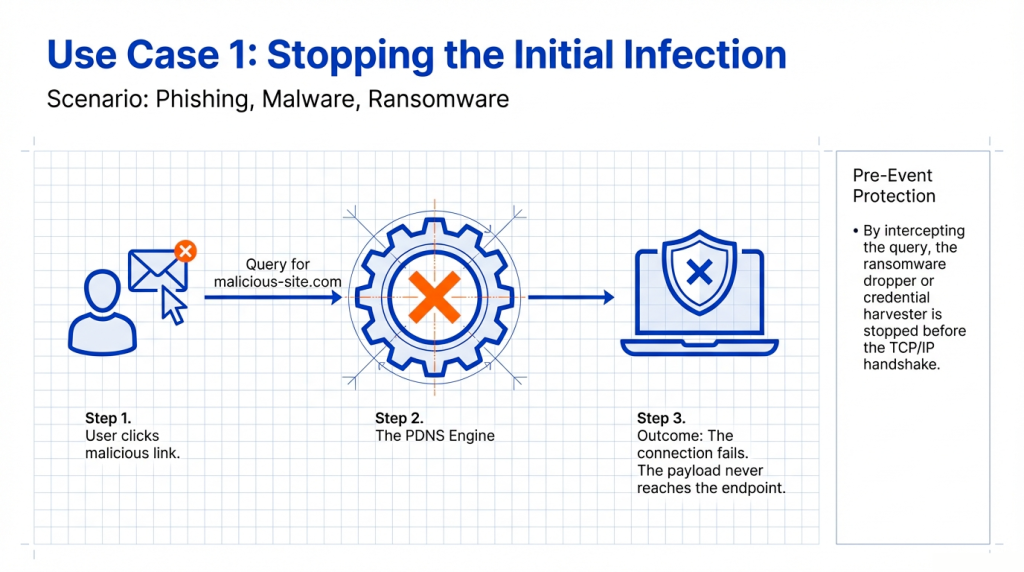
3.1. Use Case 1: Preventing Initial Infections from Malware, Phishing, and Ransomware
PDNS provides proactive, pre-event protection by blocking access to malicious domains that are essential for launching attacks. When a user clicks a phishing link or a malicious ad, the first action their device takes is a DNS query to find the server hosting the malicious content. A PDNS service intercepts this query, recognizes the domain as harmful, and blocks the connection. This action stops the attack at the earliest point in the kill chain, preventing the malicious payload—be it malware, a credential-harvesting page, or a ransomware dropper—from ever reaching the endpoint.
3.2. Use Case 2: Disrupting Attacker Command and Control (C2) Communications
Once malware successfully infects a device, its next critical step is to “phone home” to its command-and-control (C2) server. This communication almost always begins with a DNS query. PDNS is uniquely powerful here because it detects both Indicators of Compromise (IOCs)—post-event artifacts like known malicious domains—and Indicators of Attack (IOAs), which flag real-time attacker behavior. By blocking queries to known C2 domains (IOCs) and identifying anomalous beaconing patterns that suggest active C2 communication (IOAs), PDNS severs the attacker’s control channel. This isolates the compromised device, rendering the malware inert and preventing further action like data exfiltration or lateral movement.

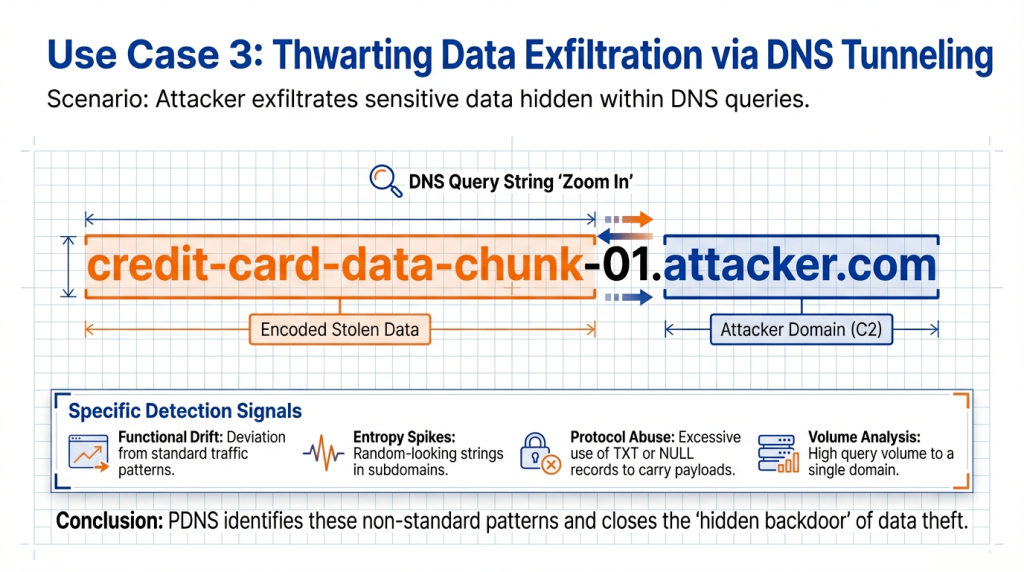
3.3. Use Case 3: Thwarting Data Exfiltration via DNS Tunneling
DNS tunneling is a sophisticated technique attackers use to bypass firewalls by encoding and exfiltrating stolen data within seemingly legitimate DNS queries. Advanced PDNS services defeat this tactic by using payload and traffic analysis to identify the specific, anomalous patterns of DNS tunneling. Instead of looking for vague anomalies, these systems are tuned to detect concrete indicators such as excessively long domain names, queries with high entropy (random-looking strings), the use of uncommon record types (TXT, NULL) to carry data, and a high query volume to a single domain. By detecting and blocking these patterns, PDNS closes this hidden backdoor.
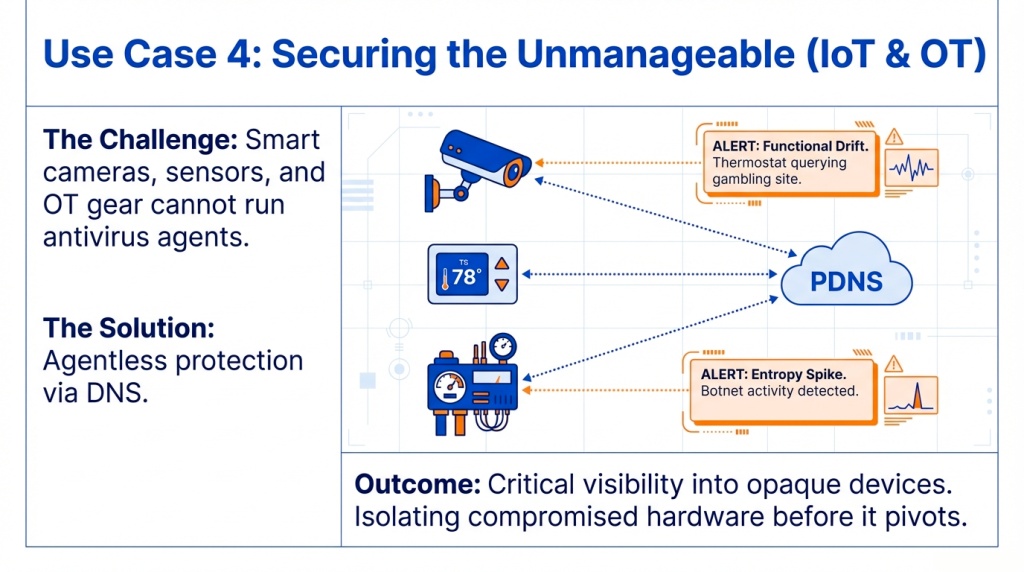
3.4. Use Case 4: Securing Unmanaged and Vulnerable IoT and OT Devices
The proliferation of Internet of Things (IoT) and Operational Technology (OT) devices creates a significant security challenge, as they often lack the ability to run traditional endpoint security agents. However, since all these devices rely on DNS, PDNS serves as an essential agentless security control. It provides critical visibility and detects compromise by identifying specific anomalies in their DNS traffic, including:
- Functional Drift: The device begins querying domains unrelated to its manufacturer or expected function.
- Entropy Spike: Queries contain randomized, high-entropy strings, a hallmark of DGA-based malware.
- Protocol Abuse: The device makes excessive requests for TXT or NULL records, suggesting data exfiltration.
Detecting these indicators allows security teams to identify and isolate a compromised device before it can be used to pivot into the broader network.
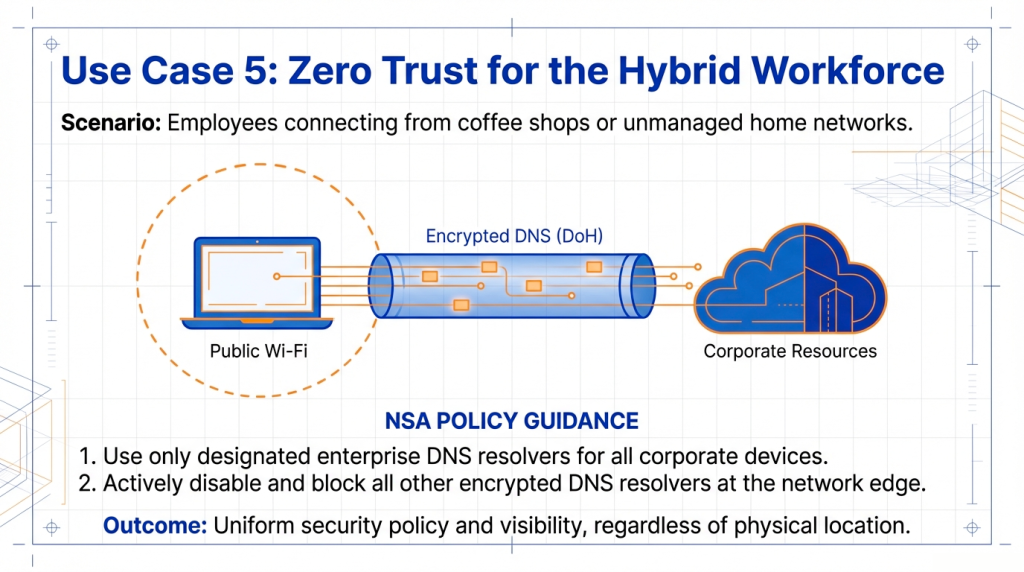
3.5. Use Case 5: Extending Consistent Protection to the Hybrid Workforce
In an era of hybrid work, employees connect from a wide variety of unsecured networks. PDNS protection can be extended to these remote workers through lightweight roaming clients or by enforcing encrypted DNS protocols like DNS-over-HTTPS (DoH). However, from an architectural standpoint, this requires strict policy enforcement. Following NSA guidance, organizations must use only designated enterprise DNS resolvers for all corporate devices and actively disable and block all other encrypted DNS resolvers at the network edge. This prevents users or malware from bypassing security controls. By enforcing a single, consistent policy, PDNS provides uniform security and visibility for all users, aligning perfectly with a modern Zero Trust architecture.
The versatility demonstrated in these use cases makes it clear that PDNS is not a niche tool but a foundational security control with broad applications.
4. Conclusion: Making DNS a Foundational Pillar of Your Defense
The Domain Name System is a foundational internet protocol that, without proper safeguards, represents a significant and often-overlooked security gap. Its inherent trust and widespread use make it a prime vector for a multitude of cyberattacks, from initial malware infection to final data exfiltration.
Protective DNS fundamentally transforms recursive DNS from a passive utility and potential liability into a proactive and powerful security asset. By filtering DNS queries against high-fidelity threat intelligence and advanced analytics, PDNS stops threats at the earliest possible moment—before a malicious connection is ever made. This simple yet profound shift strengthens an organization’s security posture, improves operational efficiency, and provides critical visibility across the entire network. For a modern, resilient security architecture, Protective DNS is a non-negotiable foundational control. Integrating it transforms a core network liability into your most efficient and pervasive security asset.